Cloud Governance
Products & Technology API Integration Software Development Cloud Governance Cloud governance is an approved framework that establishes, enforces, and monitors
Drive digital business and accelerate value at every stage of your integration and initiative.
Update legacy systems to newer approaches, frameworks and languages.
Services covering full spectrum including readiness assessment, migrations, disaster recovery and performance optimization.
Augment your team clusters on a short or long-term, temporary, and contract-to-hire basis.
We help organizations deliver high-quality software faster.
Improved operations and reduced budgetary expenditures through the reduction of directly-employed staff.
Streamline processes, boosting productivity and reducing manual efforts.
Cutting-edge solutions optimizing infrastructure, ensuring reliability, and enhancing performance.
Enhance efficiency, streamline processes, and drive strategic growth.

DevSecOps is the abbreviation for development, security, and operations. It is a development approach to platform architecture, automation, and culture that considers security a shared commitment throughout the entire software development lifecycle.
DevSecOps integrates security at every stage of SDLC, from initial design through integration, testing, deployment, and software delivery. The goal is to deliver robust and secure software applications.
Previously security operations are performed at the end of the development cycle by the different security teams and independent quality assurance (QA) testing teams. This approach is acceptable only when software update releases are scheduled once or twice a year.
However, as software engineers embraced Agile and DevOps methodologies to cut software development cycles to weeks, the traditional ‘tacked-on’ approach to security produced an unacceptable bottleneck.
DevSecOps integrates application and infrastructure security into the CI/CD pipeline, enabling development teams to address essential security concerns at Agile and DevOps speed. It addresses security issues as they arise when fixing them is more straightforward, quicker, and less expensive. It ensures IT security while following the mindset of “everyone is responsible for security.” The DevSecOps motto-“software, safer, sooner”- is achieved by automating the supply of certain products without delaying the software development cycle.
Agile development is an iterative software development methodology that aims to give teams flexibility during the development of products. While the goal of DevSecOps is to enhance an automated software development process with automated security. Both techniques demand constant development throughout the process and high levels of communication between various stakeholders.
Agile development is associated with speed — Release quickly, get feedback, fail fast, and iterate continuously. However, software developers’ outdated security tools couldn’t keep up with their increased speed. For the rapid delivery of code, security often becomes a neglected speed bump. The code progressively grows more vulnerable to leaks, breaches, and hackers.
To provide application delivery more quickly, DevOps was created as a methodology that enables software release teams and application developers to collaborate more effectively. The necessity to integrate automated security into the automated DevOps procedures led to the evolution of DevOps into DevSecOps.
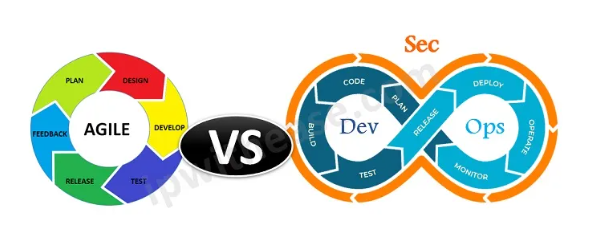
Both methodologies are complementary to one another as they have the same objective: speed and additional security. It is possible to create a well-rounded piece of software by combining the developer, quality assurance tester, security expert, and operations into a single cohort of developers called a DevSecOps team in an agile environment. This may result in improved automation and better modularity, with fewer errors. This reduces the natural resistance to change inherent in software structural and architectural design.
Organizations struggle to keep up with client demands in today’s fast-paced world. Organizations are increasingly looking to DevSecOps as a critical difference to stay competitive. But how can businesses make sure that their DevSecOps pipelines are effective? When developing a DevSecOps pipeline, organizations follow these considerations.
Container technology for the deployment of applications is currently the hot cloud technique, but it possesses security issues and vulnerabilities. Scanning for vulnerabilities, dangerous files, and compliance problems is essential as the number of container images rises. Container scanning is an important step in the DevSecOps pipeline, which identifies and avoids known vulnerabilities early in the software development life cycle.
Security control slows down the development process when security checks begin at the start of the DevSecOps pipeline. Pre-commit hooks and IDE security plug-ins can help speed up the process and provide rapid feedback by identifying security issues or potential security flaws.
In order to ensure the security of the CI/CD pipeline, quality checks like automated unit integration and acceptance tests are adopted. The build process includes checking prebuilt container images for known security issues.
Automated input validation features and checks that verify authorization, authenticity, and identification are preferred. Examples of functional security tests include password generation and authentication. In contrast, non-functional security tests look for flaws in the program’s logic and the security of the application and its infrastructure.
Access controls are deployed in CI/CD pipelines to guarantee the safety of tools and resources.
It should be secured by access keys, passwords, and other controls to make sure that only the team members who require a CI/CD pipeline have access.
SAST is a white box vulnerability screening technique that checks an application’s source code for defects. It assists in fixing fundamental security issues by finding the causes of vulnerabilities. SAST lowers the chance of application security breaches by alerting developers of potential flaws that might have been introduced into the code during development.
External packages and libraries can speed up development by enabling developers to integrate functionality without creating all the code. Still, security considerations are the foremost priority. When establishing dependencies in source code, especially if they are open source, it is imperative to manage any security dangers that can arise.
Continuous monitoring of a DevSecOps pipeline is necessary at the infrastructure, application, and network layers. This enables teams to continuously enhance their security assessments and keep up with emerging threats.
Security and speed are DevSecOps’ two key advantages. Development teams produce better, more secure code quicker and more affordable.
Delivery times are accelerated when security is incorporated early in the software development process. Before deployment, bugs are found and resolved, enabling developers to concentrate on releasing new features.
Security is a feature from the design phase onward in SDLC. A shared responsibility architecture guarantees security is tightly integrated—from creating, and deploying, to securing production workloads.
The speed with which DevSecOps handles newly discovered security vulnerabilities is a crucial advantage.
Automated testing can ensure incorporated software dependencies are at appropriate patch levels and confirm that software passes security unit testing.

As the demand for automation spreads throughout the business and IT operations, companies using DevSecOps technologies and techniques create a solid basis for digital transformation and application modernization. With Arcana, you can use advanced IT-powered automation tools, such as prebuilt workflows, to make every IT service process more intelligent. This will free up teams to concentrate on the most crucial IT problems and speed up innovation
Products & Technology API Integration Software Development Cloud Governance Cloud governance is an approved framework that establishes, enforces, and monitors

With today’s public cloud availability and security measures, coupled with optimization and automation tools, cloud migration will very likely help your business reduce IT infrastructure costs in the long run.